I’ve been fighting with the OSINT morons posting AI videos of the Iran conflict on Twitter/X, trying to pretend they’re experts on intelligence collection and analysis. Spoiler alert: they’re not, and I have all of them muted. I have, though, promised a post on OSINT and why they’re all a bunch of idiots. But that’s grown into an explanation of the entire collection types.
In this post I’ll lay out the core intelligence collection disciplines that the U.S. Intelligence Community and our allies rely on every single day. These are the -INTs – short for “INTelligence” – that get tacked on at the end of each one. And I’ll go into the OSINT fallacy at the bottom.
All of this is open-source and not classified in any way.
HUMINT – Human Intelligence
HUMINT is the collection of information from people. It is the oldest discipline and still one of the most valuable because only humans can reveal intent, plans, and internal deliberations.
Case officers – trained intelligence officers who operate under official or non-official cover – recruit and run human sources, called assets. Recruitment follows the cycle of spotting, assessing, developing, recruiting, and handling. This is the -INT that I have the least experience with, outside of talking with some former CIA field operatives while I was stationed at the NRO.
Strengths are unique. HUMINT delivers context and motivation that sensors cannot capture – Tom Clancy talks a lot about this in his books. A well-placed source inside a command structure can confirm whether a regime actually intends to attack or is bluffing. It can reveal leadership personalities, corruption, or internal dissent.
Limitations are equally real. Humans lie, exaggerate, or become double agents. Sources require constant validation. Handling them puts lives at risk – both the asset’s and the case officer’s. Compartmentalization is strict; most assets never know the full picture. Training a competent case officer takes years. The discipline is slow, expensive, and vulnerable to counterintelligence.
FININT – Financial Intelligence
Another one I don’t have much experience with – probably because most of it is outside the Pentagon and IC. FININT focuses on money flows. It tracks how adversaries fund operations, move resources, and hide transactions. The discipline exploded in importance after 9/11 when terrorist financing became a priority.
Key players are the Treasury Department, FinCEN (Financial Crimes Enforcement Network), the Office of Foreign Assets Control (OFAC), and the IRS. They use Bank Secrecy Act reporting, suspicious activity reports from banks, SWIFT data(under strict controls, and international partnerships.
Modern FININT includes cryptocurrency tracking. Blockchain analysis firms provide tools that follow wallet movements even when users try to obscure them with mixers or privacy coins. Sanctions regimes rely on FININT to identify enablers – shell companies, front businesses, hawala networks, and trade-based money laundering.
Strengths: Follow the money and you often find the network. A single transaction record can map an entire proliferation ring or terrorist cell. FININT is also highly actionable – sanctions can freeze assets overnight and disrupt operations faster than kinetic strikes in some cases.
Limitations: Adversaries adapt quickly. They shift to cash, gold, cryptocurrencies, or barter. Jurisdictions with weak banking controls create blind spots. Privacy laws and data-sharing restrictions slow collection. False positives from legitimate business complicate analysis.
GEOINT – Geospatial Intelligence
And this is the one I’m the most familiar with. For reasons I can’t tell you ;-).
GEOINT combines imagery with geospatial analysis. The National Geospatial-Intelligence Agency (NGA) leads it for the United States. It is far more than photographs. It includes maps, terrain models, elevation data, and full-motion video analysis layered with cultural and environmental context. It used to be called IMINT (IMagery Intelligence) but evolved to go beyond images to additional data related to maps.
Collection platforms range from national reconnaissance satellites (electro-optical, radar, infrared) to commercial imagery, unmanned aerial systems, and even handheld devices in the field. Synthetic aperture radar (SAR) sees through clouds and at night.
Processing turns raw pixels into intelligence products: annotated imagery, 3-D models, change detection reports, and line-of-sight analyses. Analysts measure everything from runway lengths to vehicle counts to construction rates at missile sites.
Strengths: GEOINT provides persistent, verifiable coverage of large areas. It is excellent for order-of-battle analysis, target development, and battle damage assessment. Commercial providers have democratized some capabilities – anyone with a credit card can buy sub-meter imagery today.
Limitations: Imagery shows what is there, not what people intend. Camouflage, underground facilities, and denial-and-deception tactics can fool it. Weather, orbital mechanics, and revisit rates create gaps. Over-reliance on imagery without ground truth has led to mistakes in the past.
MASINT – Measurement and Signature Intelligence
MASINT captures the unique “fingerprints” that equipment and materials emit. It measures physical phenomena – radar cross-sections, acoustic signatures, chemical spectra, seismic vibrations, radio-frequency emissions, and nuclear radiation.
The Defense Intelligence Agency’s MASINT center and service labs run the programs. Sensors include ground-based radars, seismic arrays, infrared spectrometers, and specialized satellites. MASINT detects things traditional sensors miss: the exact type of missile engine firing, the chemical composition of an exhaust plume, or the unique acoustic pattern of a submarine propeller.

Strengths: MASINT identifies specific platforms even when visual ID is impossible. It can confirm a nuclear test, distinguish a decoy from a real warhead, or track a stealth aircraft by its unique radar return characteristics. It is often the only discipline that can characterize advanced weapons systems.
Limitations: MASINT requires precise baseline signatures, which are hard to obtain. Data volumes are enormous. Environmental noise interferes. It is technically demanding and expensive to field and maintain the sensors.
SIGINT – Signals Intelligence
Another one I have a background in.
SIGINT intercepts RF signals. The National Security Agency (NSA) is the executive agent. It breaks into two main sub-disciplines: COMINT (communications intelligence) and ELINT (electronic intelligence), the former being more “listening in on phone calls” and the latter being “beeps and squeaks.”
Collection platforms include ground stations, aircraft, ships, satellites, and cyber access. The discipline covers everything from phone calls and emails to radar emissions and telemetry from missile tests.

Processing requires massive computing power to decrypt, translate, and sort petabytes of data daily. Metadata analysis often yields more than content. Direction-finding and geolocation pinpoint emitters.
Strengths: SIGINT delivers high-volume, timely data. It can reveal communications patterns, command relationships, and technical capabilities. When codes are broken or access is gained, it provides unparalleled insight.
Limitations: Encryption is everywhere and getting stronger. Adversaries use fiber optics, burst transmissions, and low-probability-of-intercept waveforms. Legal and policy restrictions limit collection inside the United States. Partners provide critical access but bring their own constraints.
OSINT – Open Source Intelligence
This is where everyone is getting in trouble on Twitter.
OSINT collects information from publicly available sources. It has existed for decades but exploded with the internet. The Open Source Center (now part of the CIA’s Directorate of Digital Innovation) and service OSINT cells lead it. Yes, the IC uses OSINT all of the time. But more on that in a sec.
Sources include foreign media, academic papers, commercial databases, social media, satellite imagery from companies like Planet or Maxar, corporate filings, job postings, and even video games or public tenders. Analysts use web scraping, geospatial tools, language translation software, and network analysis.
Strengths: OSINT is cheap, fast, and legal. It provides context and baseline data that classified sources often lack. It can tip off where to focus scarce collection assets. In the social media era, OSINT can track individuals, units, and movements in near real time.
Limitations: Public information can be disinformation. Verification is critical and time-consuming. Adversaries manipulate open sources deliberately. Language and cultural barriers remain. The sheer volume of data overwhelms manual analysis – automation helps but introduces errors.
What the OSINTers Get Wrong
No -INT operates in isolation. The intelligence community uses an all-source approach. GEOINT might spot unusual construction at a site. MASINT confirms the signature of a new missile system. HUMINT provides the internal rationale. SIGINT captures the command traffic. OSINT supplies open confirmation and context. FININT traces the funding.
All of these -INTs are collection methods…which are just one part of the intelligence cycle!
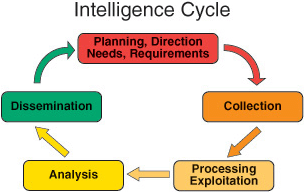
In the American intelligence community, each one of these phases are conducts by highly-paid professionals. Collection is just one of many steps a piece of intelligence – a video posted on Twitter (OSINT), a satellite image (GEOINT), a new Russian radar waveform (SIGINT) – goes through before it goes to decision makers (Dissemination) who then give new intelligence needs out to the collection element.
The OSINTers are trying to do the entire cycle themselves! And in isolation, more or less!

This is why they all come across as total idiots on Twitter and elsewhere. They may (or may not, I’ve seen a lot of ARMA footage) be able to locate images or videos that are relevant to the current Iran conflict, but that’s just “collection” – none of them are qualified experts to determine what is happening, where it’s happening, and its relevance to an intelligence question. None of them are experts or trained analysts, none of them have experience or the relevant accompanying piece(s) of classified information to make sense of the deluge of intelligence coming in.

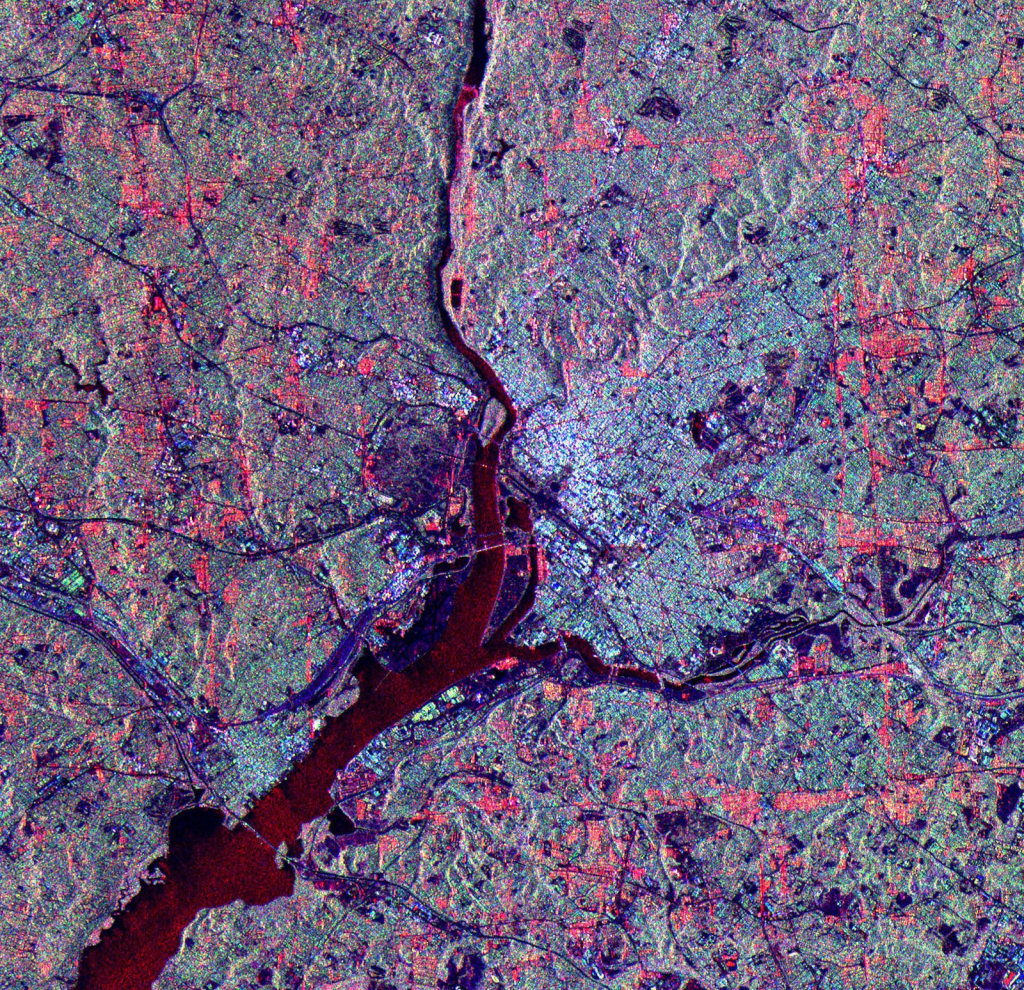
Can you make heads or tails of what’s happening in that image? Probably not, but a trained intelligence analyst can, and they are also able to derive secondary and tertiary information from it, with varying levels of confidence, before sending it to an aggregator to be included in a brief. The OSINTers are trying to do the jobs of 4-5 people and are failing miserably. Their editorialization just makes things worse, and the majority of them are incredibly biased in some direction, compounding the issue.
It pains me to say this, but especially for the current conflict, the mainstream news sources – and official USG ones – are the best sources of information. Iran and its allies have done a great job of disinformation and the OSINTers are lapping it up, unfortunately.
For Writers
Do your research, understand that this isn’t Jason Bourne (as much as I love Jason Bourne), and that it’s a slow, often boring process. Tom Clancy and John Le Carre get much of it right, most other authors do not. And someone who “knows” will be able to spot you getting it wrong from a mile away…but may not tell you, because they can’t! There’s plenty of open-source stuff to go through, make sure you get the details right if you get down in the weeds.
Leave a comment